Phishing or Business Email Compromise (BEC) is a method of gathering personal information using deceptive e-mails and websites. It is basically a cyber attacker that uses fraudulent email as a tool. The cyber attacker’s goal is to trick the email recipient into believing that the message is genuine and needs to be actioned . For example a request from the bank to update password, or a note from a colleague in the company to click a link or download an attachment…
..
Method of Attack

These messages aim to trick the user into revealing important data often a username and password that the attacker can use to breach a system or account. The classic version of this scam involves sending out an email with convincing social engineering to look like a message from a major bank; by spamming out the message to millions of people, the attackers ensure that at least some of the recipients will be customers of that bank. The victim clicks on a link in the message and is taken to a malicious site designed to resemble the bank’s webpage, and then hopefully enters their username and password. The attacker can now access the victim’s account.
Malicious code.

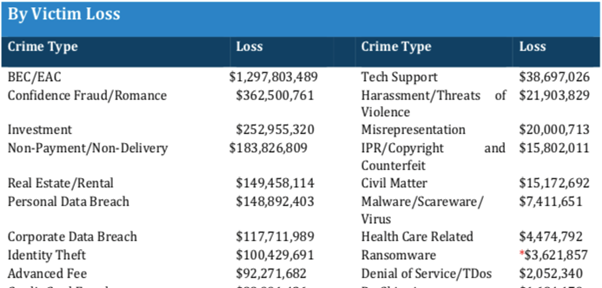
Like a lot of spam, these types of phishing emails aim to get the victim to infect their own computer with malware. Often the messages are “soft targeted” they might be sent to an HR staffer with an attachment that purports to be a job seeker’s resume, for instance. These attachments are often .zip files, pdf, or Microsoft Office documents with malicious embedded code. Phishing emails account to 94% of the most common form of malicious code, ransomware – Trendmicro. Infact The 2018 Internet Crime report (ICR) has BEC with the greatest financial loss at $1.298 billion.
How to stop Phishing
Staff members need to be aware of phishing attacks. Security awareness helps your organization to resist online scams. The best defense against phishing emails is the email gateway, blocking 99% of unwanted email at the gateway, including malicious attachments, content, and URLs – long before an end user ever sees them. Also, web filtering is a defense mechanism that filters and blocks infected URLs.

Additionally, file sandboxing isolates and runs files in a controlled environment without affecting application or platforms in which they are running. It ensures malware files are removed. Most of importantly appropriate training and education is critical for ensuring that all your employees know how to spot and deal with these types of email messages.
Training
Training matters because ‘it just takes one employee and one click to cause serious financial and reputational damage to your organization. Making sure employees are aware of the threat posed by a cyber-security breach is no long a nice-to-have. It is a must-have.’ TrendMicro So would you employees fall for a phishing scam? . Prepare the employees to be more cautious and lets win this fight against phishing.